Elliptic Curve Cryptography via OpenSSL
Consider the following scenario: you’re chatting with your buddies on a social media platform, but you’d like to keep your conversations private. This is just one of the ways public key cryptography is making communication safer and more secure with End to End encryption.
Have you ever wondered how your online passwords and financial transactions are kept secure? It’s all thanks to the power of public key cryptography, and two of the most widely used algorithms are RSA and ECC.

C**ontents:IntroductionElliptic CurvesWorking algorithm of ECCFeatures of ECCHow are keypairs generated? Along with Encryption and Decryption?Demonstration of generation of key Pairs using OpenSSL.
Elliptic Curve Cryptography (ECC) is a type of public-key cryptography used to secure data transmission over the internet. Unlike traditional encryption algorithms, which use large prime numbers, ECC relies on the properties of elliptic curves to generate secure keys. It is a popular encryption algorithm used in various applications, including digital signatures, secure key exchange, and secure communication protocols.
ECC is based on the mathematical properties of elliptic curves, which are curves defined by a set of points that satisfy a specific equation. These curves have unique properties that make them ideal for encryption, including their ability to generate large prime numbers that are difficult to factorize. ECC’s security is based on the difficulty of computing the discrete logarithm problem, which involves finding the exponent of a base point on the elliptic curve.
Despite its relatively recent discovery, ECC has gained popularity due to its efficiency and strong security guarantees. It requires less computation and generates shorter keys than traditional encryption algorithms, making it well-suited for resource-constrained environments such as mobile devices and embedded systems.
In this blog, we will explore the key concepts of ECC and how it works, its advantages and disadvantages, and its applications in various fields.
Elliptic Curve Cryptography (ECC) is a public key cryptography that generates keys and safeguards data using elliptic curves. In clear terms, it’s a technique of ensuring that no one can access your communications or data without your consent.
To encrypt a message, the sender uses the recipient’s public key to generate a shared secret key, which is then used to encrypt the message using a symmetric key encryption algorithm. To decrypt the message, the recipient uses their private key to generate the same shared secret key, which is then used to decrypt the message.
In terms of generating a key pair mathematically, this involves choosing a random private key, then using the elliptic curve equation to calculate the corresponding public key. Point addition involves finding the slope of a line connecting two points on the curve and using this slope to find the third point of intersection on the curve.
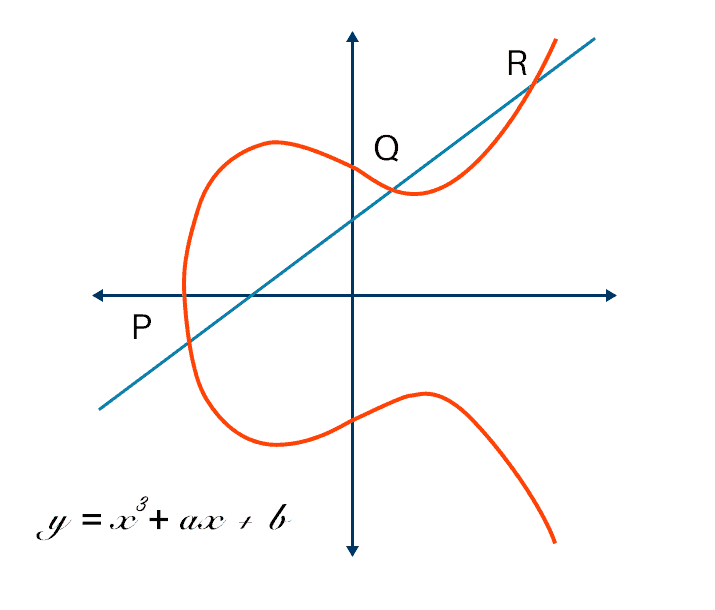
A mathematical curve known as an elliptic curve may be defined by the equation y² = x³ + ax + b where a and b are constants. The curve has a distinguishing feature that makes it valuable in cryptography. ECC is regarded as safe because it is difficult to solve the discrete logarithm problem in the underlying elliptic curve group.
An elliptic curve over a field is a set of points (x, y) satisfying an equation of the form:
y² = x³ + ax + b where a and b are constants, and
4a³ + 27b² ≠ 0 is to ensure that the curve is nonsingular.
The working of the ECC algorithm can be explained in the following steps:
Key Pair Generation: The first step in the ECC algorithm is the generation of public and private key pairs. The private key is kept secret and known only to the owner, while the public key is shared with other parties.
Elliptic Curve Equation: An elliptic curve equation is used to define a set of points on a curve. This equation can be in the form of y² = x³ + ax + b, where a and b are constants that define the curve, and x and y are the coordinates of the points.
Point Addition: Points on the curve are added using a set of rules that define the operation. When two points are added, the resulting point is also on the curve. The addition operation is commutative, meaning that the order of addition does not matter.
Scalar Multiplication: Scalar multiplication involves multiplying a point on the curve by a scalar value, which is a large integer. This operation involves adding the point to itself multiple times, using the point addition rules.
Encryption and Decryption: To encrypt a message, the sender uses the recipient’s public key to generate a shared secret key. This key is then used to encrypt the message using a symmetric key encryption algorithm. To decrypt the message, the recipient uses their private key to generate the same shared secret key, which is then used to decrypt the message.

Here are some features of the Elliptic Curve Cryptography (ECC) algorithm:
Strong security: Comparatively speaking to other encryption methods, ECC offers robust security with reduced key sizes. Because of this, it works well in contexts with limited resources, such as those seen in mobile and Internet of Things devices.
Efficient performance: ECC is suited for use in applications that require rapid and secure encryption and decryption because it provides efficient performance for cryptographic operations.
Key agility: Key management is made simple and agile using ECC. When a key breach is suspected or when users need to be added or removed from a system, it may be helpful to rapidly generate new keys.
Small key sizes: ECC keys are much smaller than other encryption algorithms such as RSA. For example, a 256-bit ECC key offers equivalent security to a 3072-bit RSA key.
Support for various security levels: ECC supports a range of security levels, depending on the choice of the elliptic curve and key size used. This makes it flexible and adaptable to different security requirements.
Resistance to quantum attacks: ECC is believed to resist attacks by quantum computers, which are a potential threat to other encryption algorithms such as RSA and AES.

Let’s better understand how key pairs are generated and Encryption & Decryption.
— To generate a key pair in elliptic curve cryptography, we need to follow the steps given below:
Select an elliptic curve and a point on that curve: We first choose an elliptic curve equation and a point on that curve as a starting point. The curve equation is in the form y² = x³ + ax + b, where a and b are constants. The point (x,y) should be a point on the curve and it will serve as our starting point.
Choose a private key: The private key is a randomly generated large number that is kept secret by the owner. It is usually denoted by the letter d.
Generate the public key: To generate the public key, we perform scalar multiplication of the chosen point with the private key. The public key is the resulting point on the curve and is denoted by Q = dP, where P is the chosen point and Q is the public key.
Distribute the public key: The public key Q is shared with other parties to allow them to encrypt messages to the owner of the private key.
The security of the key pair depends on the difficulty of calculating the private key d from the public key Q, which is believed to be a computationally difficult problem known as the elliptic curve discrete logarithm problem (ECDLP).
Encryption and Decryption: After the key pair generation and establishing the elliptic curve equation, encryption using ECC involves the following steps:
The sender and receiver agree upon the same elliptic curve equation and a base point on that curve.
The sender generates a random number, which is kept secret and used as a scalar value.
The scalar value is used to multiply the base point on the curve, resulting in a new point.
The sender uses the x-coordinate of the new point as the shared secret key.
The message is encrypted using a symmetric encryption algorithm, such as AES, with the shared secret key.
The encrypted message is sent to the receiver along with the public key, which contains the base point and the elliptic curve equation.
The receiver uses their private key to compute the same shared secret key by multiplying the base point with their secret scalar value.
The receiver decrypts the message using the shared secret key and the same symmetric encryption algorithm used by the sender.
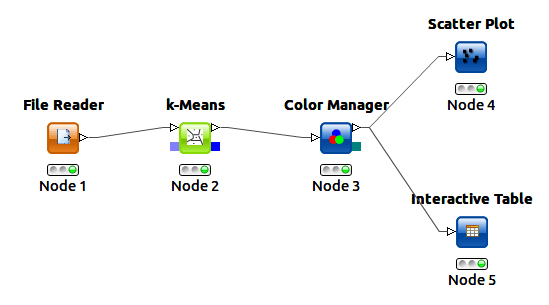
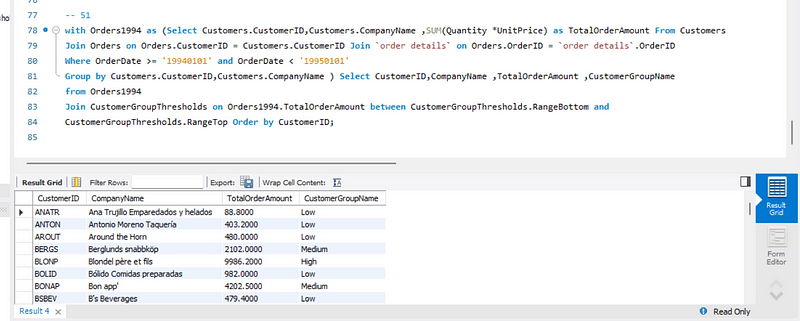
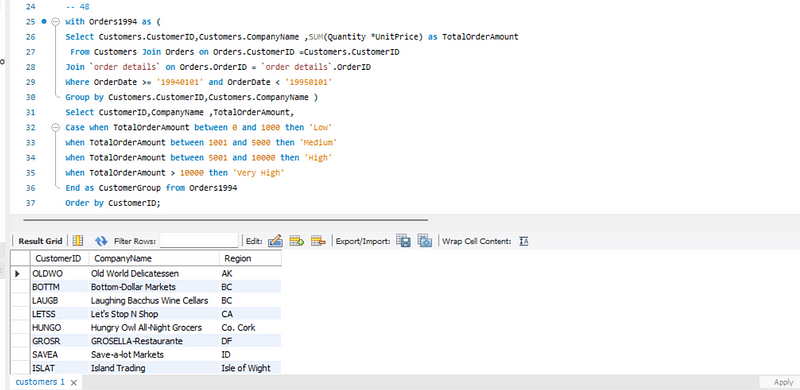
To demonstrate ECC in action, we provided an example of generating a key pair using OpenSSL, showcasing the implementation of the ECC algorithm working.
- To list the available elliptic curves that can be used in OpenSSL.
openssl ecparam -list_curves

2. To generate a new EC private key using the secp256k1 curve and save it to a file named ec-privatekey.pem. To display the contents of the ec-privatekey.pem file on the terminal.
openssl ecparam -name secp256k1 -genkey -noout -out ec-privatekey.pem
cat ec-privatekey.pem

3. To derive the corresponding public key from the private key stored in the ec-privatekey.pem file, and save it to a new file named ec-pubkey.pem.
openssl ec -in ec-privatekey.pem -pubout -out ec-pubkey.pem
cat ec-pubkey.pem


4. To display the details of the EC private key stored in the ec-privatekey.pem file on the terminal.
openssl ec -in ec-privatekey.pem -text -noout

5. To display the details of the EC public key stored in the ec-pubkey.pem file on the terminal.
openssl ec -in ec-pubkey.pem -pubin -text -noout

6. To output the parameters of the secp256k1 elliptic curve to a file named secp256k1.pem.The cat secp256k1.pem command is used to display the contents of the secp256k1.pem file on the terminal.
openssl ecparam -name secp256k1 -out secp256k1.pem cat secp256k1.pem
openssl ecparam -in secp256k1.pem -text -param_enc explicit -noout

This is how the generation of key pairs is done using OpenSSL in the terminal/command Line.
I hope this article was informative and provided you with the details you required. If you have any questions while reading the blog, message me on Instagram or LinkedIn.
Special credits to my team member: Krisha Amlani
Thank You…